
[ad_1]
Why it issues: The shift to a hybrid work mannequin with many workers working from residence has opened up a brand new avenue for malicious actors. Security researchers warn {that a} subtle malware marketing campaign has been focusing on North American and European residence and small workplace networks by means of router malware that has largely gone unnoticed till not too long ago.
Last yr, cyberattacks towards company networks reached record-setting ranges by way of frequency and dimension, largely due to the Log4J vulnerability that was left unpatched by many organizations for a number of months. Earlier this month, a brand new and hard-to-detect malware was found on Linux-based techniques that had been stealing credentials and enabling distant entry for malicious actors.
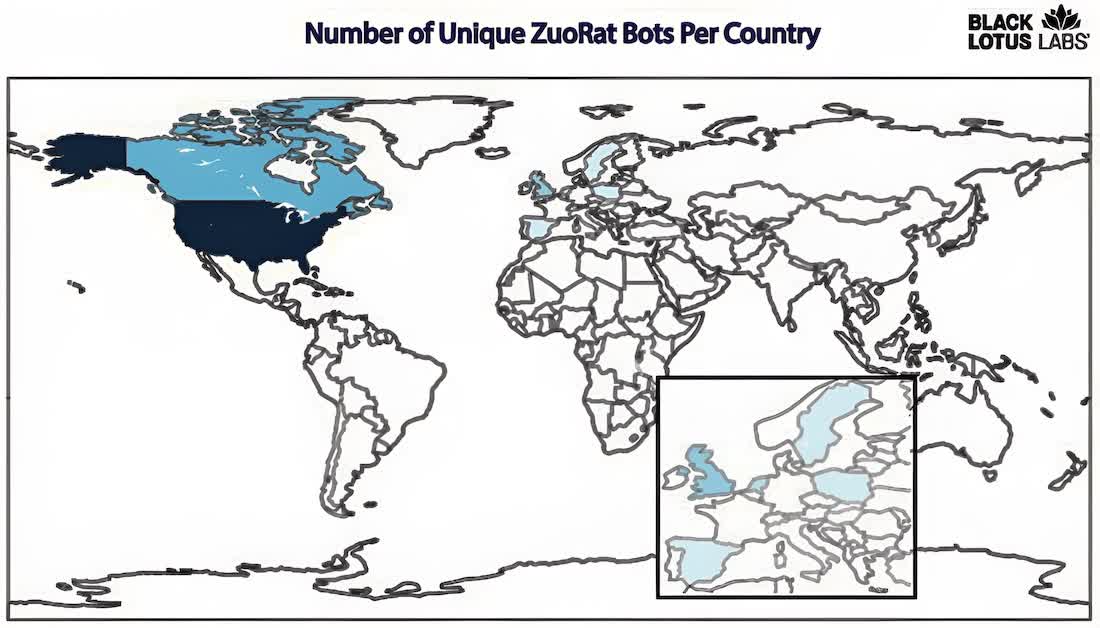
In the same vein, a brand new stealthy distant entry trojan dubbed ZuoRAT has been detected by safety researchers at Lumen Black Lotus Labs. The group that found the brand new risk believes it has been infecting a variety of residence and small workplace (SOHO) routers throughout Europe and North America with malware that may take management of gadgets working Windows, Linux, or macOS.
This has been occurring since at the least December 2020, and ZuoRAT is believed to be a part of a much wider malware marketing campaign that took benefit of the sudden and big shift to distant work and examine. The malicious actors selected to assault consumer-grade routers with exploitable firmware that’s not often monitored and patched, if ever.
Black Lotus Labs researchers declare they’ve recognized at the least 80 targets to date, and located ZuoRAT to be surprisingly subtle for malware that is meant to compromise SOHO routers offered by Asus, Netgear, DrayTek, and Cisco.
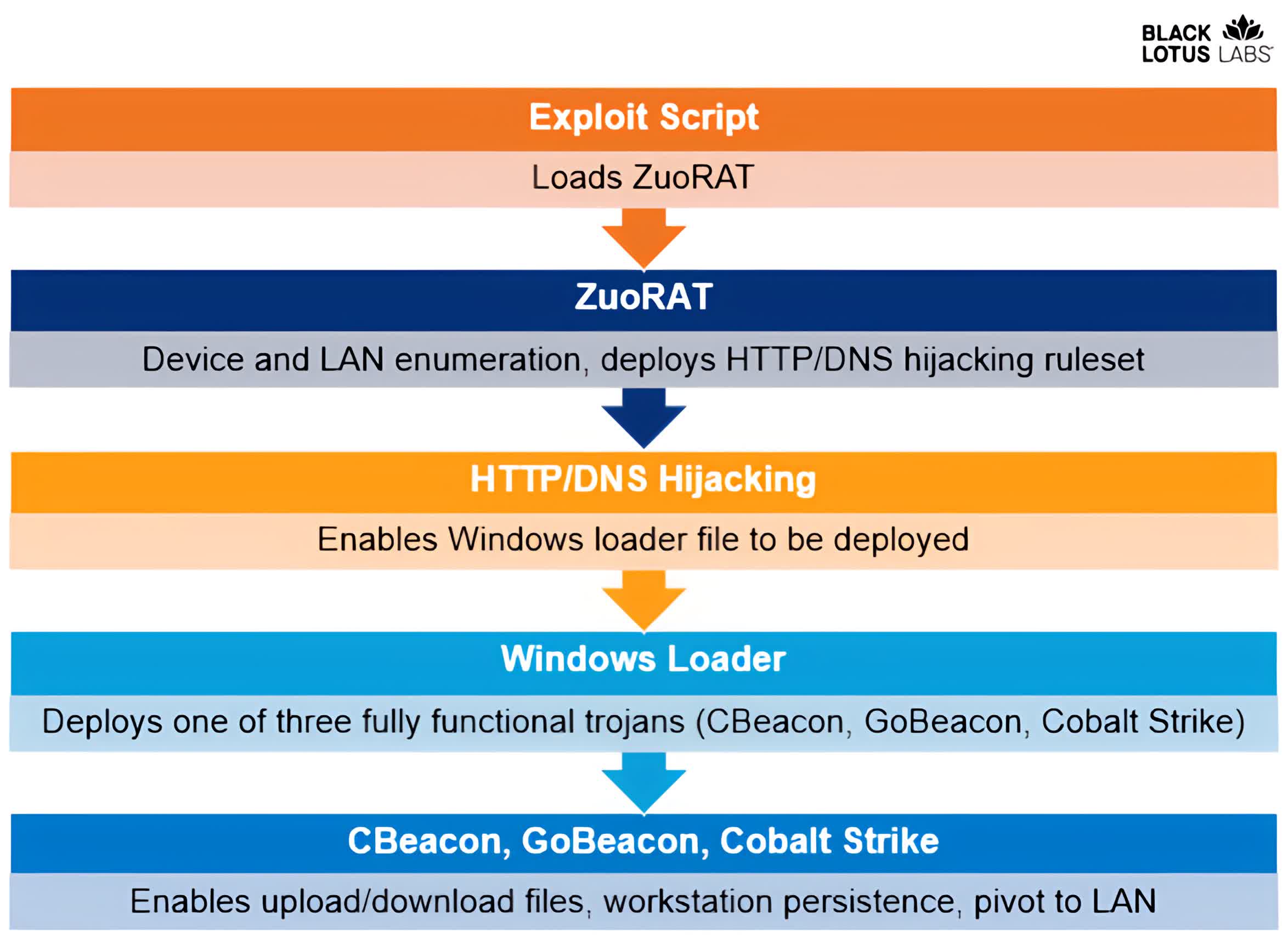
The malware marketing campaign leverages at least 4 completely different items of malicious code, and ZuoRAT is worryingly just like different custom-built malware written for the MIPS structure such because the one behind the notorious Mirai botnet of yesteryear.
Once ZuoRAT makes its manner right into a router, the malicious actors can use DNS and HTTP hijacking to put in extra items of malware dubbed Beacon and GoBeacon, in addition to the widely-used Cobalt Strike hacking instrument.
Researchers defined the marketing campaign is aimed toward a number of US and Western European organizations and the attackers have gone to excessive lengths to cover their exercise by means of obfuscated, multistage C2 infrastructure. And whereas it is solely a suspicion at this level, the analyzed information signifies the attackers could also be working within the Chinese province of Xiancheng utilizing information heart infrastructure from Tencent and Alibaba’s Yuque collaboration instrument.
The excellent news is that router malware like ZuoRAT might be flushed out with a easy reboot of the contaminated gadget since that might wipe its recordsdata which reside in a brief folder. A manufacturing unit reset could be even higher, but when the contaminated gadgets additionally include the opposite items of malware they will not be as straightforward to take away.
Security analysts and system directors can discover extra particulars concerning the technical points of the ZuoRAT marketing campaign, together with indicators of compromise and potential prevention instruments, by studying the complete report and consulting the Black Lotus Labs GitHub.
[ad_2]


