
[ad_1]
In temporary: Researchers have found a comparatively new worm that infects Windows PCs by means of a compromised exterior laborious drive. Although they’ve been staying it for a number of months and know the way it works, they’re not sure of its finish recreation. Aside from the insidious nature of its operation, its late-stage duties are nonetheless unknown.
Red Canary analysts have disclosed a cluster of malware exercise that makes use of a worm unfold by way of exterior USB drives. The malware employs the “QNAP worm,” which cyber-intelligence agency Sekoia described again in November 2021. However, Red Canary detected it in a few of its know-how and manufacturing clients’ networks and tracked it since September below the codename Raspberry Robin.
Raspberry Robin spreads when customers join an contaminated USB drive to their pc. The worm, disguised as an LNK file, then makes use of Windows cmd.exe to launch a malicious file. It then makes use of Microsoft Standard Installer (msiexec.exe) to connect with command-and-control (C2) servers — normally susceptible QNAP units. It then makes use of TOR exit nodes to cowl its tracks.
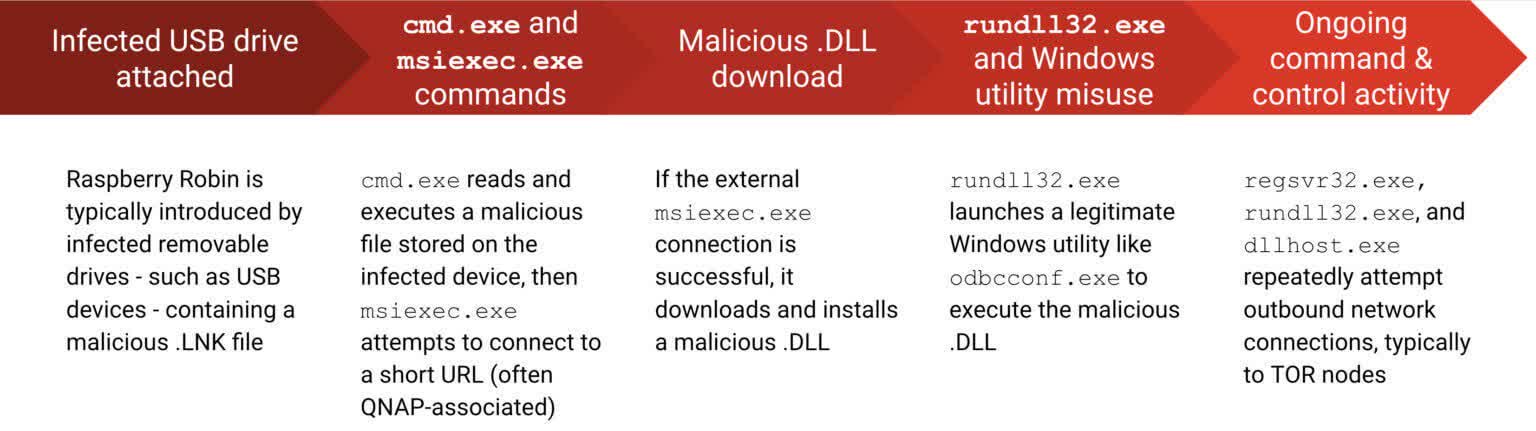
Red Canary suspects that Raspberry Robin establishes persistence by putting in a malicious DLL file from the C2 servers. The malware then launches the DLL utilizing two utilities included in Windows: fodhelper (a Windows setting supervisor) and obdcconf (an ODBC driver configuration software). The former bypasses User Account Control, and the latter executes and configures the DLL.
However, the researchers admit that is only a working speculation. They do not exactly know what the DLLs do, nor have they found out the way it spreads to USB drives.
“First and foremost, we do not know the way or the place Raspberry Robin infects exterior drives to perpetuate its exercise, although it is doubtless this happens offline or in any other case outdoors of our visibility,” mentioned Red Canary. “We additionally do not know why Raspberry Robin installs a malicious DLL.”
It can also be unclear what the QNAP worm’s final function is. Other than the way it works, the researchers haven’t seen any “late-stage exercise” that will profit the operators.
Image credit score: Red Canary
[ad_2]


