What simply occurred? The United States Attorney’s Office for the Central District of California not too long ago introduced the seizure of the WorldWiredLabs community area and supporting infrastructure. The operation, coordinated by a number of international locations and regulation enforcement businesses, stopped the unfold of the NetWire Remote Access Trojan (RAT). The malware is disguised and marketed as a authentic administrative software, which is utilized by malicious actors to realize unauthorized entry to focused techniques.
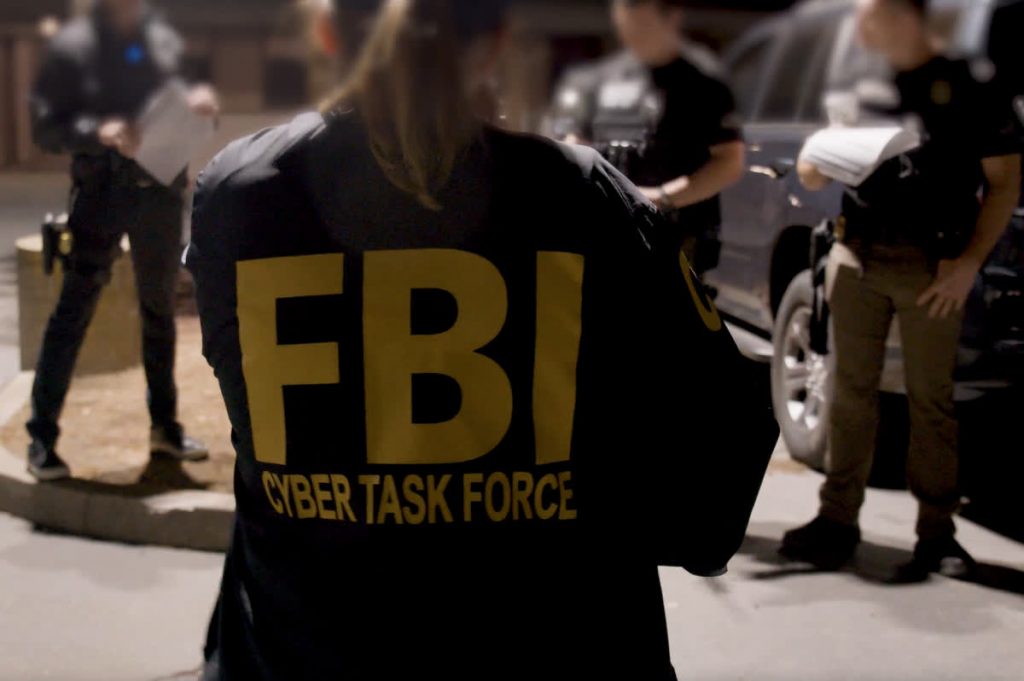
It took years of investigation, remark, and planning by regulation enforcement businesses all over the world to efficiently nook RATs. Federal authorities in Los Angeles have served a warrant to grab the worldwiredlabs.com net area used for the sale and distribution of NetWire malware. In addition to the seizure, authorities additionally arrested a Croatian nationwide recognized as the location’s administrator. The now-seized web sites show a coordinated effort between the US, Croatia, Switzerland, Australia and different Europol-affiliated authorities.
damaged!a coordinated #lawenforcement Action ðÂÂð··ð¨ðÂð¦ðºðºð¸ has been eliminated #cable Remote entry to Trojan infrastructure.
� ½” The essential suspect was arrested.#cable is a licensed commodity RAT provided in underground boards to non-technical customers to hold out their very own legal actions.
— EC3 (@EC3Europol) March 10, 2023
The FBI’s preliminary investigation started in 2020, when investigators bought a duplicate of the suspected malware and turned it over for additional evaluation. According to the arrest warrant’s abstract of potential causes, FBI investigators had been capable of efficiently entry the web site, pay for a subscription plan, and obtain a NetWire RAT package deal to be used. Once acquired, an FBI laptop scientist makes use of NetWire’s builder software to configure an occasion to check the malware’s performance in opposition to a chosen take a look at machine. NetWire by no means tried to confirm that these analyzing the software program really had entry to the goal machine.
Once configured, FBI laptop scientists confirmed that the software program allowed NetWire customers to entry recordsdata, shut purposes, retrieve authentication data, observe keystrokes, execute instructions, and take screenshots, all with out alerting the focused consumer. These options, behaviors, and lack of notifications are the calling playing cards of a standard RAT assault, designed to draw malicious actors intent on benefiting from in any other case unsuspecting customers.
There are a number of methods organizations and customers might help defend themselves from falling sufferer to RATs and different social engineering-driven assaults. An earlier INFOSEC article offered an in depth overview of how NetWire works and offered customers and organizations with suggestions for defending in opposition to such assaults. These embody:
- Train customers on potential phishing patterns and the right way to cope with them
- Be conscious of emails from unfamiliar senders or sources and emails with suspicious attachments
- Verify the supply by different means earlier than opening or downloading content material
- Use antimalware, antivirus, or different endpoint safety software program
- Keep all software program and working system recordsdata up to date
Assistant Director Donald Alway, who oversees the FBI’s Los Angeles Field Office, emphasised the significance of NetWire malware elimination. “By eradicating the NetWire RAT, the FBI impacted the legal cyber ecosystem.” Alway’s assertion additionally highlighted the truth that “…the worldwide partnership that led to the arrest in Croatia additionally eliminated a well-liked laptop hijacking instruments to perpetuate international fraud, information breaches and cyber intrusions by menace teams and cybercriminals.”


