
[ad_1]
Why it issues: An email-focused safety agency launched a weblog submit detailing a phishing assault concentrating on unsecured American Express and Snapchat websites. The recognized exploit makes use of a recognized open redirect vulnerability that enables risk actors to specify a redirect URL, driving site visitors to fraudulent websites designed to steal consumer data.
Maryland-based safety agency INKY Security tracked assault exercise associated to the vulnerability from mid-May via mid-July. The phishing assault depends on a recognized open redirect vulnerability (CWE-601) and well-liked model recognition to deceive and harvest credentials from unsuspecting Google Workspace and Microsoft 365 customers.
The assaults focused unsecured websites from Snapchat and American Express. Snapchat-based assaults resulted in additional than 6,800 assaults over a two-and-a-half-month interval. The American Express-based assaults have been way more efficient, affecting over 2,000 customers in simply two days.
Malicious actors have taken benefit of open-redirect vulnerabilities affecting AMEX & Snapchat domains to ship #phishing emails concentrating on Google Workspace and Microsoft 365 customers.”
— INKY (@InkyPhishFence) August 4, 2022
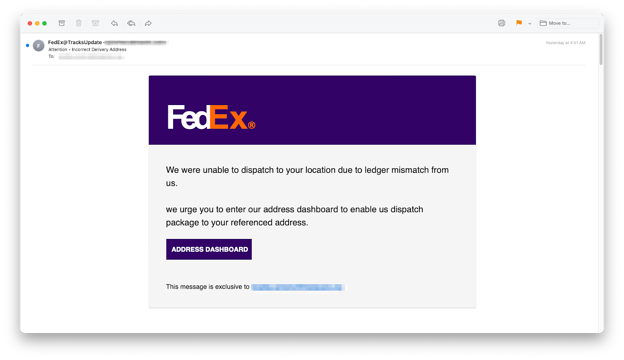
The Snapchat-based emails drove customers to fraudulent DocuSign, FedEx, and Microsoft websites to reap consumer credentials. Snapchat’s open redirect vulnerability was initially recognized by openbugbounty greater than a yr in the past. Unfortunately, the exploit nonetheless seems to be unaddressed.
American Express seems to have remediated the vulnerability, which redirected customers to an O365 login web page much like the one which the Snapchat-based assaults used.
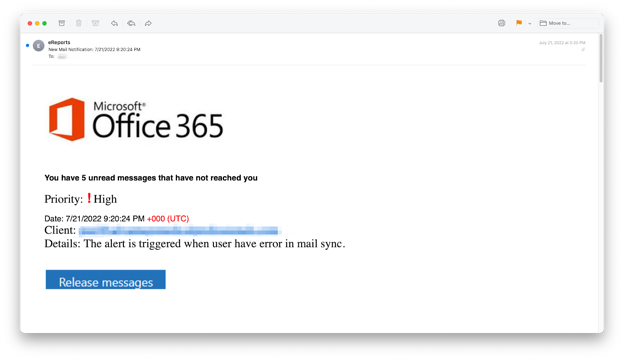
This particular phishing assault makes use of three main strategies: model impersonation, credential harvesting, and hijacked accounts. Brand recognition depends on recognizable logos and logos to create a way of belief with the potential sufferer resulting in the consumer’s credentials being entered into and harvested from the fraudulent web site. Once harvested, hackers can promote the stolen data to different criminals for revenue or use the knowledge to entry and acquire the sufferer’s private and monetary data.
Open redirect vulnerabilities do not are likely to get the identical degree of care and a spotlight as different recognized exploits. Additionally, most danger publicity is on the consumer slightly than the positioning proprietor. The weblog submit gives extra background and steerage to assist customers keep protected and preserve their information out of the mistaken fingers. These ideas assist customers determine key phrases and characters which will point out if a redirect is happening from a trusted area.
Image credit score: INKY Security
[ad_2]


