
[ad_1]
Why it issues: For IT admins and cybersecurity groups, a ransomware assault is an important race towards time to detect and include harm whereas salvaging what’s left of an organization’s knowledge belongings. But how a lot response time is there when such an incident happens? Not lots it appears, as revealed by ransomware testing of ten candidates, the place LockBit led the pack by encrypting practically 100,000 recordsdata on a Windows Server machine in simply over 4 minutes.
The ransomware encryption velocity check carried out by Splunk concerned ten samples from ten ransomware households, which have been run on 4 totally different ‘sufferer’ profiles. From a complete of 400 check runs, a pattern from LockBit operating on a Windows Server 2019 machine emerged because the quickest ransomware, encrypting all 53GB of check knowledge in simply 4 minutes and 9 seconds.
This check knowledge consisted of 98,561 recordsdata, comprising pdfs, and excel and phrase paperwork. Meanwhile, the ransomwares have been examined on a Windows 10 and Windows Server 2019 machine and included samples from REvil, Darkside, Babuk, Maze, LockBit, and several other others. LockBit not solely had the quickest pattern, but in addition got here out first total when it comes to median period.
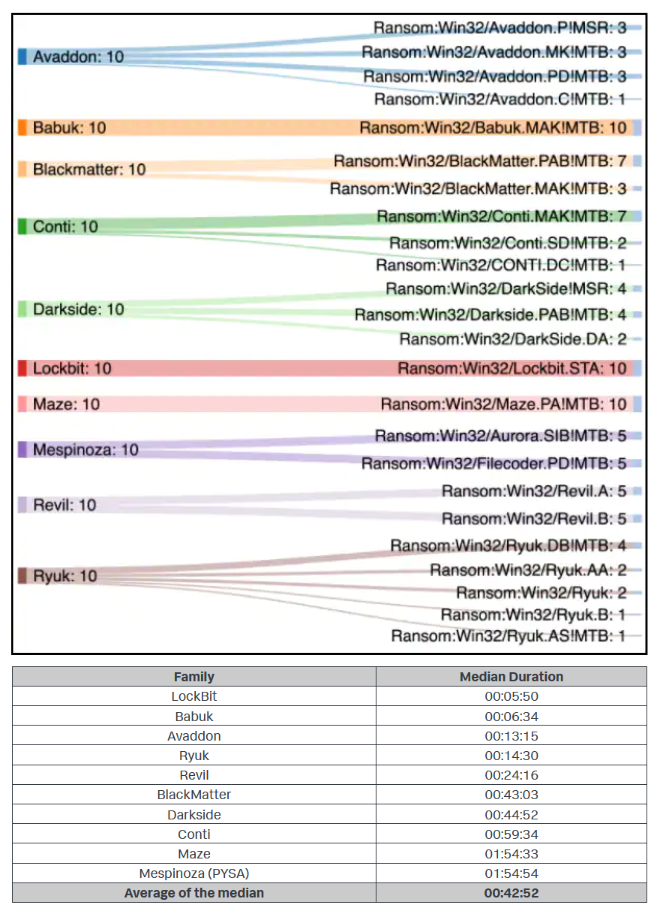
The apparently named ‘Babuk’ ransomware emerged second total, although it had its popularity spoiled considerably by having the slowest particular person pattern that took over three and a half hours for file encryption.
Splunk additionally shared a whitepaper (requires a enterprise e-mail to obtain), providing a complete take a look at this analysis. As for methods to undertake in case of a ransomware assault, the corporate advises utilizing multi-factor authentication, community segmentation, centralized logging, and preserving techniques patched.
[ad_2]


