
[ad_1]
TL;DR: A Russian modular botnet known as Cyclops Blink is hijacking Asus routers worldwide, reportedly in an try and construct a military of compromised routers to be used in cyberwarfare. The hackers need to use the weak gadgets as command-and-control (C&C or C2) servers.
Cyclops Blink is a Kremlin-linked malware that has existed since 2019. It is tied to the elite Sandworm hacking group. According to UK’s National Cyber Security Centre (NCSC), it initially focused WatchGuard Firebox gadgets. Sandworm was linked to different well-known cyber-attacks, just like the NotPetya ransomware, which has induced billions of {dollars} price of injury globally since June 2017, and the BlackEnergy malware behind the Ukrainian blackouts of 2015-16.
Researchers with Trend Micro word that Cyclops Blink casts a large web when it comes to the gadgets it infects, with no particular concentrate on high-value authorities or diplomatic entities. Hackers compromised a few of the contaminated gear greater than two and a half years in the past.
Cyclops Blink makes an attempt to determine persistence for risk actors on the system, creating a degree of distant entry to compromised networks. Due to its modular design, it may possibly simply be up to date to focus on new gadgets. It has not too long ago gained a brand new module permitting it to assault Asus routers.

Trend Micro notes that the targets don’t seem like of specific worth for cyberwarfare.
“It ought to be famous that these victims don’t seem like evidently beneficial targets for both financial, navy, or political espionage. For instance, a few of the stay C&Cs are hosted on WatchGuard gadgets utilized by a regulation agency in Europe, a medium-sized firm producing medical gear for dentists in Southern Europe and a plumber within the United States … The objective of this botnet continues to be unclear: Whether it’s supposed for use for distributed denial-of-service (DDoS) assaults, espionage, or proxy networks stays to be seen. But what is clear is that Cyclops Blink is a sophisticated piece of malware that focuses on persistence and the power to outlive area sinkhole makes an attempt and the takedown of its infrastructure.”
Researchers imagine there’s one other vendor with compromised firmware, however sadly, they can not determine the seller but.
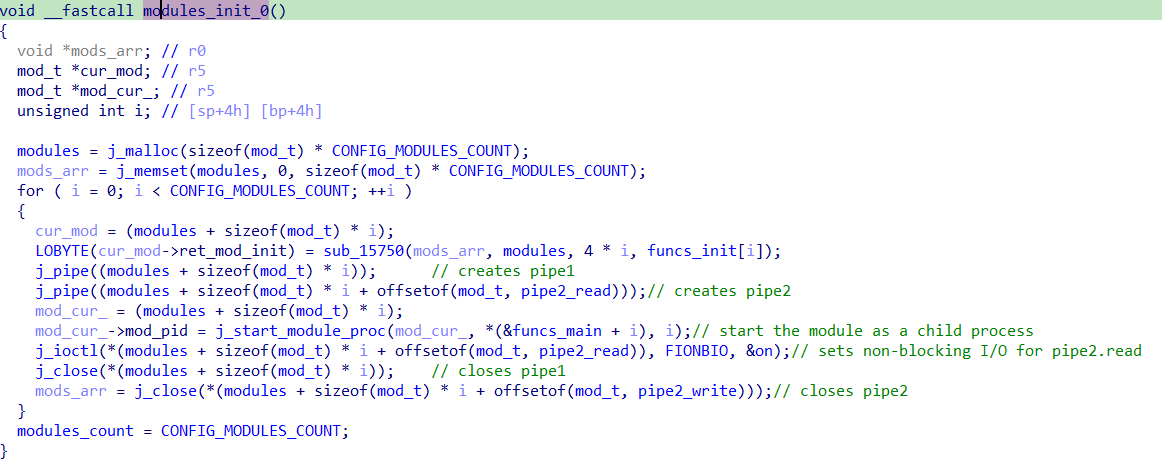
Cyclops Blink makes use of hard-coded TCP ports to speak with C&C servers. For each port, it makes a brand new rule within the Netfilter Linux kernel firewall to permit output communication to it. Once a connection is established, the malware initializes an OpenSSL library, and its core element then executes a set of hard-coded modules. The malware then pushes numerous parameters to those modules, which return information that the core element encrypts utilizing OpenSSL features earlier than sending it again to the C2 server.
Trend Micro believes the malware is the successor to the VPNFilter malware from 2018. It, too, was designed to contaminate routers and networked gadgets to siphon information and compromise them for future use.
The new Asus module is constructed to entry and substitute a router’s flash reminiscence. The botnet reads 80 bytes from the flash reminiscence, writes it to the principle communication pipe, after which waits for a command with the information wanted to exchange the content material. A second module gathers information from the contaminated system and sends it to the C2 server. A 3rd module, “file obtain (0x0f),” downloads information from the web utilizing DNS over HTTPS (DoH).
Affected Asus mannequin numbers and their firmware particulars are as follows:
- GT-AC5300
- GT-AC2900
- RT-AC5300
- RT-AC88U
- RT-AC3100
- RT-AC86U
- RT-AC68U
- AC68R
- AC68W
- AC68P
- RT-AC66U_B1
- RT-AC3200
- RT-AC2900
- RT-AC1900P
- RT-AC1900P
- RT-AC87U (EOL)
- RT-AC66U (EOL)
- RT-AC56U (EOL)
As of publication, Asus has not launched new firmware updates however has launched the next mitigation directions:
- Reset the system to manufacturing facility default: Login into the net GUI, go to Administration → Restore/Save/Upload Setting, click on the “Initialize all of the setting and clear all the information log,” after which click on Restore button.”
- Update to the most recent accessible firmware.
- Ensure the default admin password has been modified to a safer one.
- Disable Remote Management (disabled by default, can solely be enabled through Advanced Settings).
The three fashions designated as EOL (finish of life) are not supported and will not obtain any firmware safety updates. Asus recommends shopping for a brand new one.
The associated safety advisory for WatchGuard community gadgets will be discovered on WatchGuard’s web site.
[ad_2]


